“Without security, there is no business in a digital world”
How does your daily routine as the CISO at the Migros Cooperative Federation look like?
My daily routine is very diverse. Generally, it consists of various topic-specific meetings, design decisions, and often the coordination of projects.
Where does Migros place its focus when organizing cybersecurity?
We take a risk-oriented approach and carefully consider the benefits of setting priorities. This allows us to organize information security in a targeted manner.
“Challenges such as an increased need for coordination arise from a decentralized structure like that of the Migros Cooperative Federation, which we address through clear process ownership.”– Lukas Ruf
Migros, as a cooperative federation, is fundamentally organized in a very decentralized manner. How does this affect the organization of cybersecurity? What are the specific challenges?
The organization of cybersecurity must take this into account. Therefore, our processes always incorporate the federal approach as a basic principle and aim for the scalability of activities. As with any distributed system, a decentralized structure brings the usual challenges such as an increased need for coordination, which we address through clear process ownership.
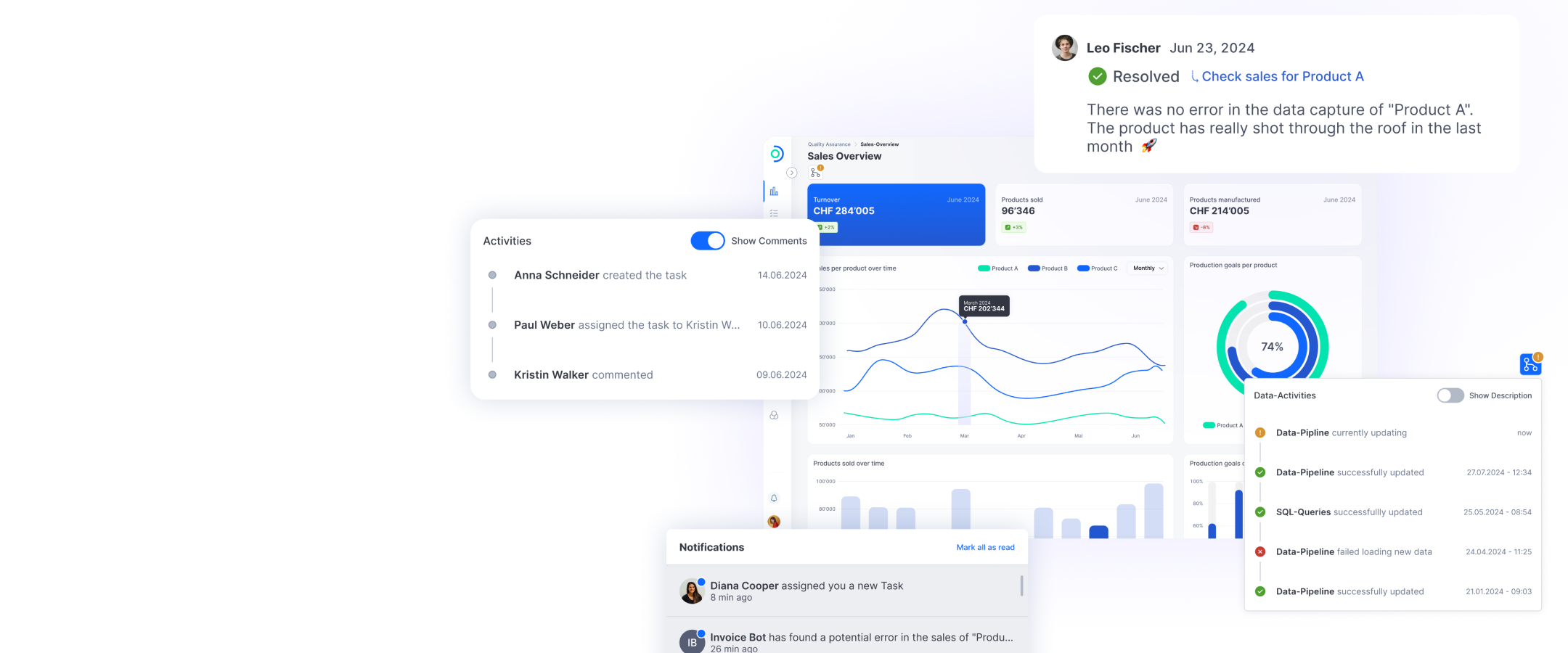
Modern cloud architectures are very powerful and flexible, but on the other hand, applications consist of complex networks of different components and services, whose lifecycle must be kept track of. What strategies does Migros pursue in this regard?
In the field of information security, maintaining an overview is one of the challenges that must be mastered through the use of modern cloud architectures. Depending on the specific cloud model, this task can be more difficult than before. Particularly with SaaS applications provided by third parties, we rely on the transparency of the providers.
“When it comes to raising employee awareness about cyber risks, it is more effective to conduct continuous, smaller training sessions rather than large training blocks. Equally important is the regular exchange within our Security & Risk Community.”– Lukas Ruf
Information security famously starts with employees. How does Migros raise awareness among its employees about the risks, and which measures have proven to be particularly effective or ineffective?
Our employees are the most valuable asset when it comes to information security. To raise awareness, we launched the 'Migros Security Culture' program, which sensitizes employees within the community in a targeted manner. In addition to targeting specific groups, we've found that regularly conducted smaller sessions are more effective than infrequent large training blocks. Equally important is regular exchange within our Security & Risk Community. We organize this in a hybrid format: we meet in person twice a year and once virtually for a community event. Additionally, we have a 'Security & Risk Talk' twice a month where we discuss advancements. These initiatives aim to enhance employees' awareness of cyber risks and cultivate a robust security culture within our organization.
New technologies require new security measures. How do you address new risks, such as those posed by AI or the emergence of quantum computing?
We closely monitor technological developments and address new risks in a highly structured manner, evaluating their implications for us and determining how Migros can respond effectively. Depending on the nature of the risk, we assign dedicated teams to these specific issues, providing me with decision-making frameworks. For instance, when it comes to quantum safety, we developed a roadmap to prepare for the Q-Day. This roadmap ensures that we proactively integrate necessary measures into product lifecycles to protect encryption values, avoiding last-minute retrofitting during a major exercise like the Q-Day.
“To be prepared for Q-Day, we have developed a roadmap. This allows us to implement necessary measures to protect encryption early and within the framework of the product lifecycle.”– Lukas Ruf
Security measures are often perceived as a necessary evil or even as an innovation barrier. How would you personally assess their importance within the company and how do you address these perceptions?
My stance on this issue is diametrically opposed to that perception: In a digital world, business cannot exist without security, as both business processes and customer interactions would suffer significantly without adequate protection. To counter these perceptions, it's crucial to regularly emphasize the value created by cybersecurity and support this with risk assessments.